320M domains · Real-time · Predictive
See threats at the infrastructure layer. Before they reach your users.
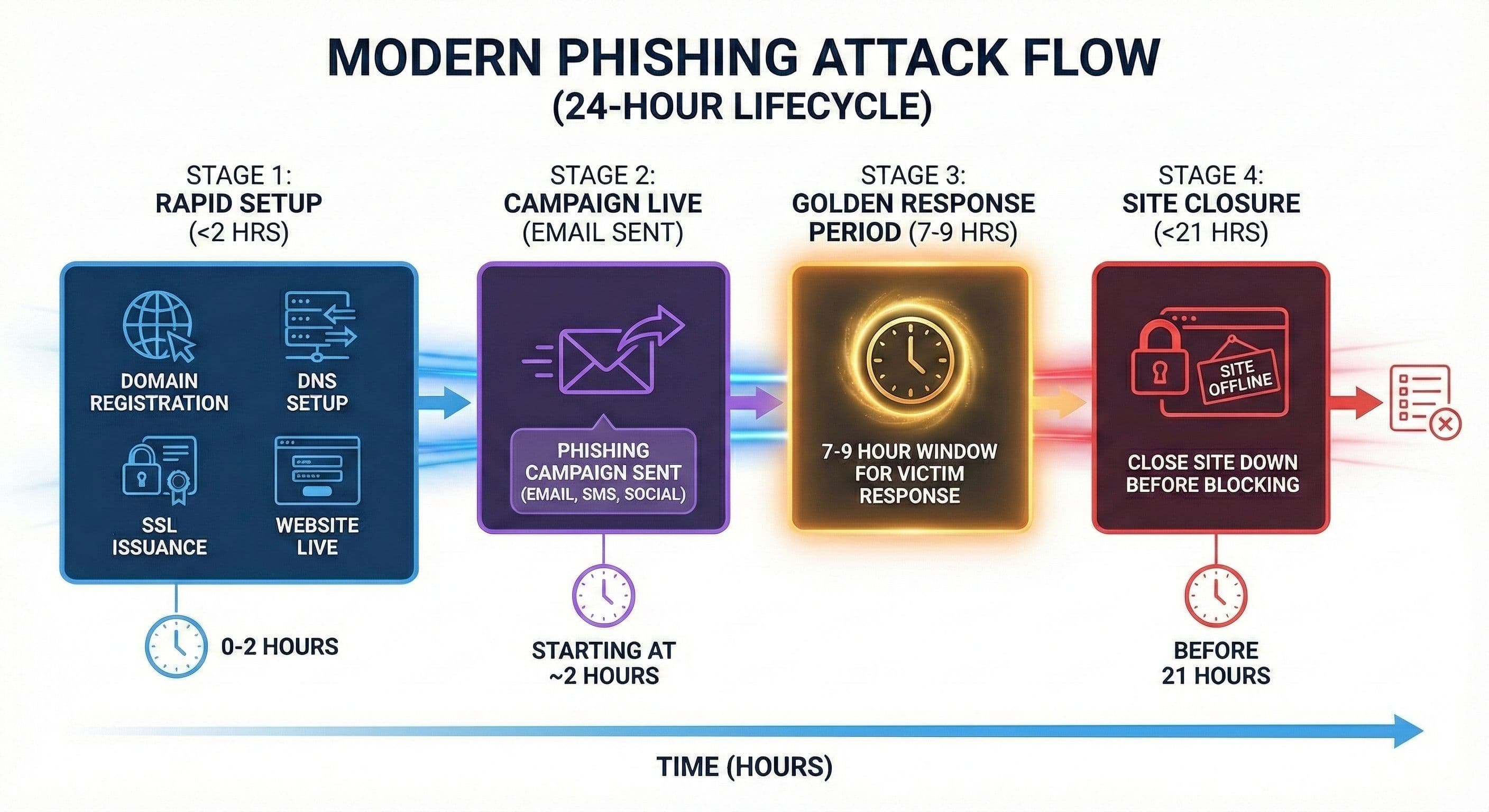
60% of phishing sites go live within 2 hours. Most threat intelligence arrives 8–12 hours later. Datazag maps the internet's infrastructure — domains, DNS, hosting, routing, certificates — and identifies attacks as they're assembled. Hours before blocklists. Before campaigns launch.
Modern Threats Start with Infrastructure
Attackers don’t begin with emails or websites.
They begin by assembling infrastructure.
Domains, DNS, certificates, and routing are configured before content appears — often within minutes.
Our Approach:
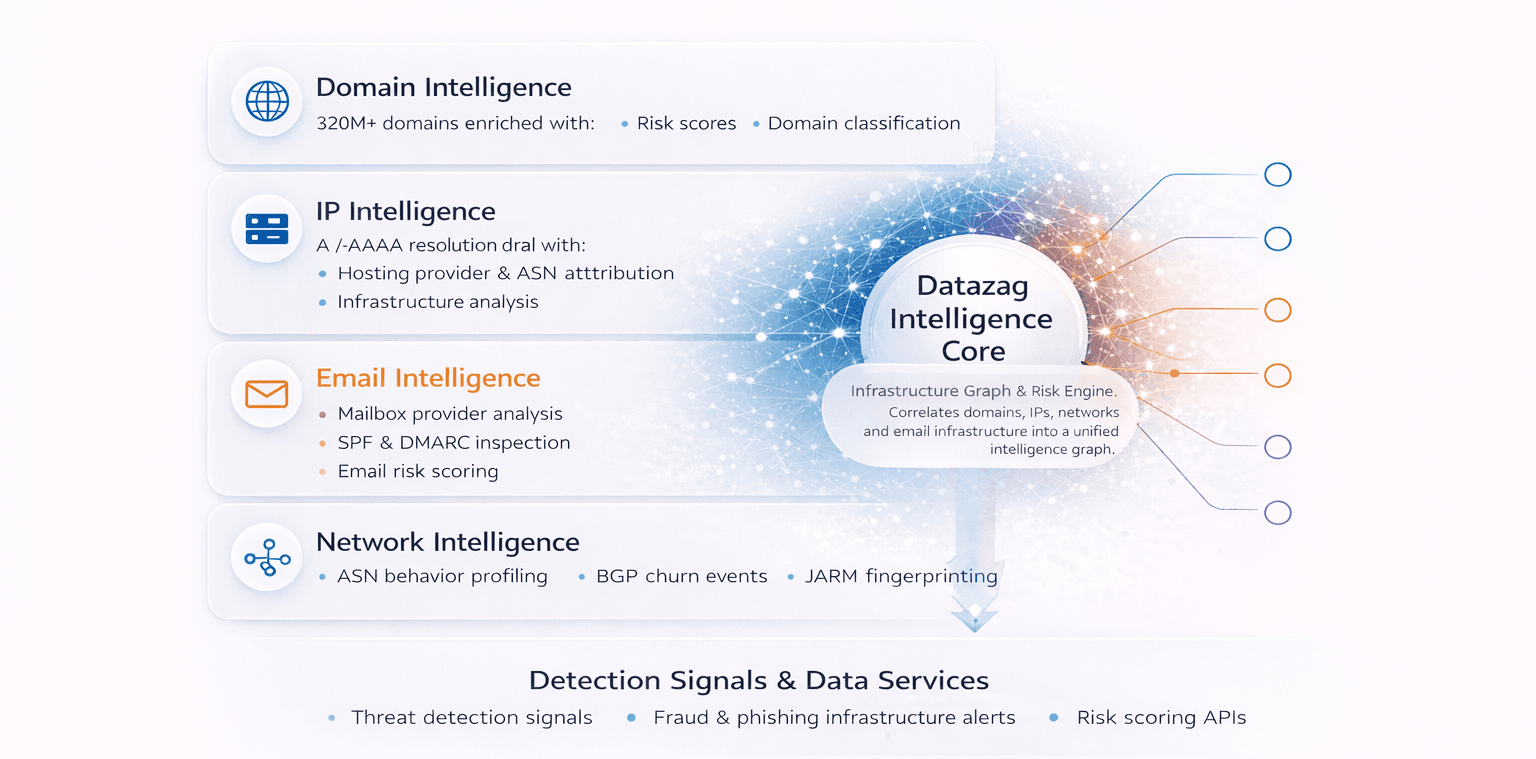
One Intelligence Core. Four Layers
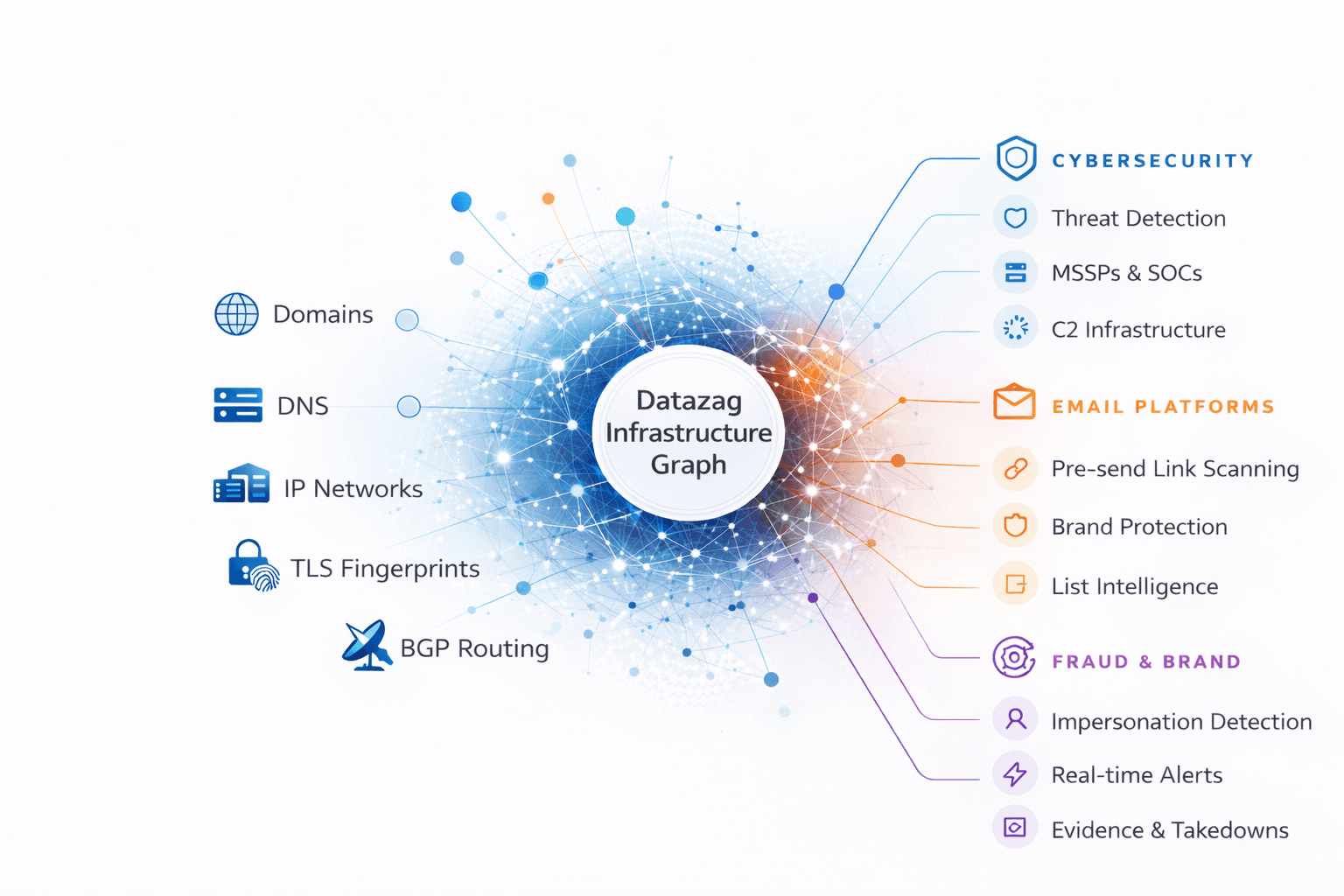
Datazag operates a continuously refreshed intelligence backbone spanning 320M+ domains and global infrastructure.
Delivered via API or webhooks, designed for automated enforcement — not manual investigation. Plus access to our 320M+ domain database using Cloud marketplace shares formatted as Iceberg or Delta data lakes
Our Approach:
The gap
From Creation to Enforcement in <60 Seconds
We monitor the global infrastructure layer so you don't have to. No portals, no manual hunting—just high-fidelity data delivered where you already work.
- Global IP & hosting infrastructure mapping
- ASN network ownership
- TLS fingerprints revealing malicious infrastructure
- Internet routing monitoring
- Explainable risk scores based on infrastructure fingerprints
- Alerts updated over time with evidence
- Early warning before attack start
- Cloud Data Lakes: Native shares for Snowflake, Databricks, and BigQuery.
- Real-time Webhooks: Alerts sent to your SOAR (Splunk, Sentinel) in under a minute.
- High-Speed API: Query our 315M+ domain database on demand.
We detect suspicious infrastructure during registration, DNS setup, and SSL issuance — reducing triage workload and false positives by prioritising the domains that matter.
Infrastructure intelligence is more than just phishing attack detection
Our 315M enriched domains with risk scores, hosting intelligence, and real-time updates can support your other cyber security needs
Fraud & Platform Abuse Detection
Detect newly created bad actor infrastructure commonly used in scams and account fraud.
Security Operations Enrichment
Feed early-warning domain signals into SIEM?SOAR workflows.
Vendor & Supply Chain Monitoring
Continuously monitor third-party domains for emerging risks.
Email Security and Deliverability
Identify spoofed sender domains and suspicious infrastructure including SPF and DMARC records.
Threat Intelligence and Hunting
Detect C2 infrastructure and threat actor domain patterns.
Attack Surface Management
Discover external assets and shadow IT infrastructure, plus sub-domain sprawl.